Computer systems leak secrets and techniques. Not simply by way of invasive advert monitoring, data-stealing malware, and your ill-advised oversharing on social media, however by way of physics. The actions of a tough drive’s elements, keystrokes on a keyboard, even the electrical cost in a semiconductor’s wires produce radio waves, sound, and vibrations that transmit in all instructions and might—when picked up by somebody with sufficiently delicate tools and sufficient spycraft to decipher these indicators—reveal your personal information and actions.
This class of spying strategies, initially codenamed TEMPEST by the Nationwide Safety Company however now encompassed within the extra basic time period “side-channel assaults,” has been a identified downside in laptop safety for near eight many years, and it is one which america authorities fastidiously considers in securing its personal categorized info. Now a pair of US lawmakers are launching an investigation into how susceptible the remainder of us are to TEMPEST-style surveillance—and whether or not the US authorities must push system producers to do extra to guard Individuals.
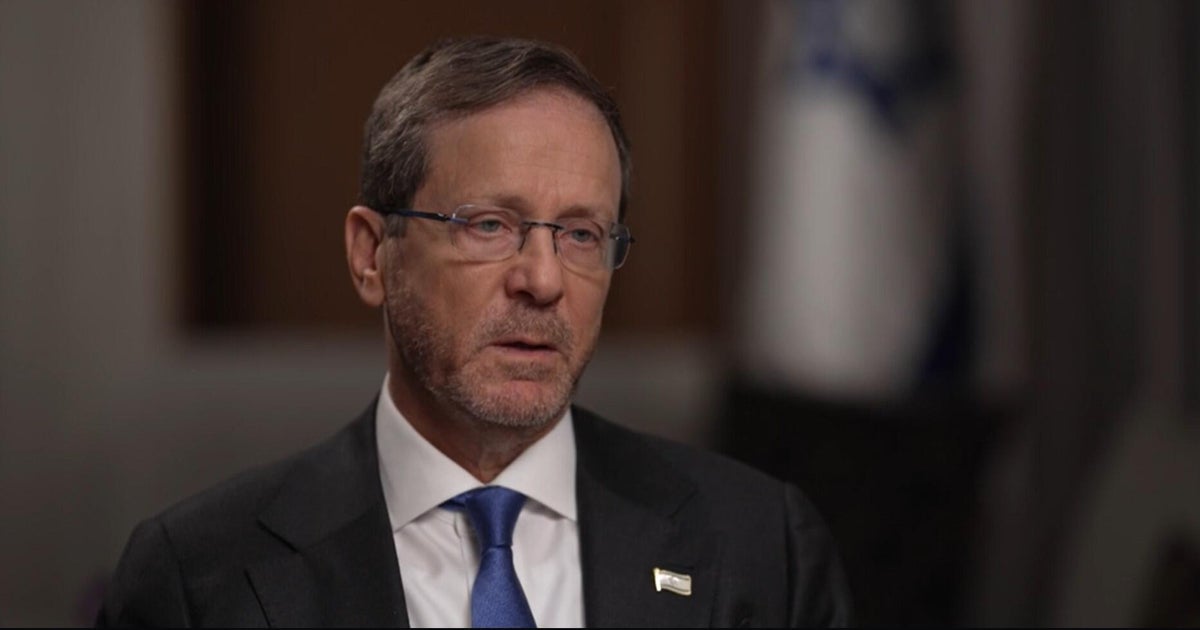
On Wednesday, Senator Ron Wyden and Consultant Shontel Brown launched a letter they despatched to the Authorities Accountability Workplace (GAO) demanding an investigation into the vulnerability of recent computer systems to TEMPEST-style side-channel assaults, the monitoring and deciphering of unintended emanations from PCs, telephones, and different computing units to surveil their operations. Within the letter, Wyden and Brown write that these types of spying “don’t simply pose a counterintelligence menace to the US authorities, however these strategies will also be exploited by adversaries towards the American public, together with to steal strategically necessary applied sciences from US corporations.”
Together with the letter, Wyden and Brown additionally commissioned a newly launched Congressional Analysis Service report in regards to the historical past of TEMPEST and the modern menace posed by related side-channel assaults. It describes the US authorities’s efforts to guard its units from these spy strategies, together with using remoted, radio-shielded areas for securely accessing secret info often called a Delicate Compartmented Data Facility, or SCIF. In the meantime, the federal government has “neither warned the general public about this menace, nor imposed necessities on the producers of client electronics, akin to smartphones, computer systems and laptop equipment, to construct technical countermeasures into their merchandise,” Wyden and Brown level out within the letter. “As such, the federal government has left the American folks susceptible and in the dead of night.”
Wyden and Brown’s letter ends by urging GAO to overview an inventory of TEMPEST-related points: the dimensions of the trendy privateness menace of side-channel assaults, the “value and feasibility” of implementing protections towards them in fashionable units, and “potential coverage choices to mitigate this menace towards the general public, together with mandating system producers add countermeasures to their merchandise,” suggesting that Congress may apply strain to tech corporations so as to add extra defenses to the units they promote.
Simply how sensible side-channel assaults like TEMPEST are towards fashionable computing units—and the way usually they’re really used within the wild by hackers and spies—stays removed from clear. However the opportunity of such assaults has been taken critically by the US authorities since as early because the Nineteen Forties, when Bell Labs found that machines it bought to the US army for encrypting messages produced legible indicators on an oscilloscope on the opposite facet of the lab.
The Bell Labs machines had been transmitting clues in regards to the internal workings of army cryptography within the radio waves created by their elements’ electromagnetic cost. A declassified NSA report from from 1972 later described the issue of the company’s categorized computer systems transmitting “radio frequency or acoustic power.” The report added: “These emissions, like tiny radio broadcasts, could radiate by way of free house for appreciable distances” of a half mile or extra if the sign is performed by way of close by supplies like energy strains or water pipes.